Venustech: Embrace Evolution with AI or Face Demise
![]() 04/15 2026
04/15 2026
![]() 537
537
Anthropic has unveiled a highly potent model named Claude Mythos.
Without human expert intervention, this model managed to penetrate the cybersecurity defenses of nearly all major companies and even discovered a long-standing vulnerability in FreeBSD, an operating system renowned for its security.
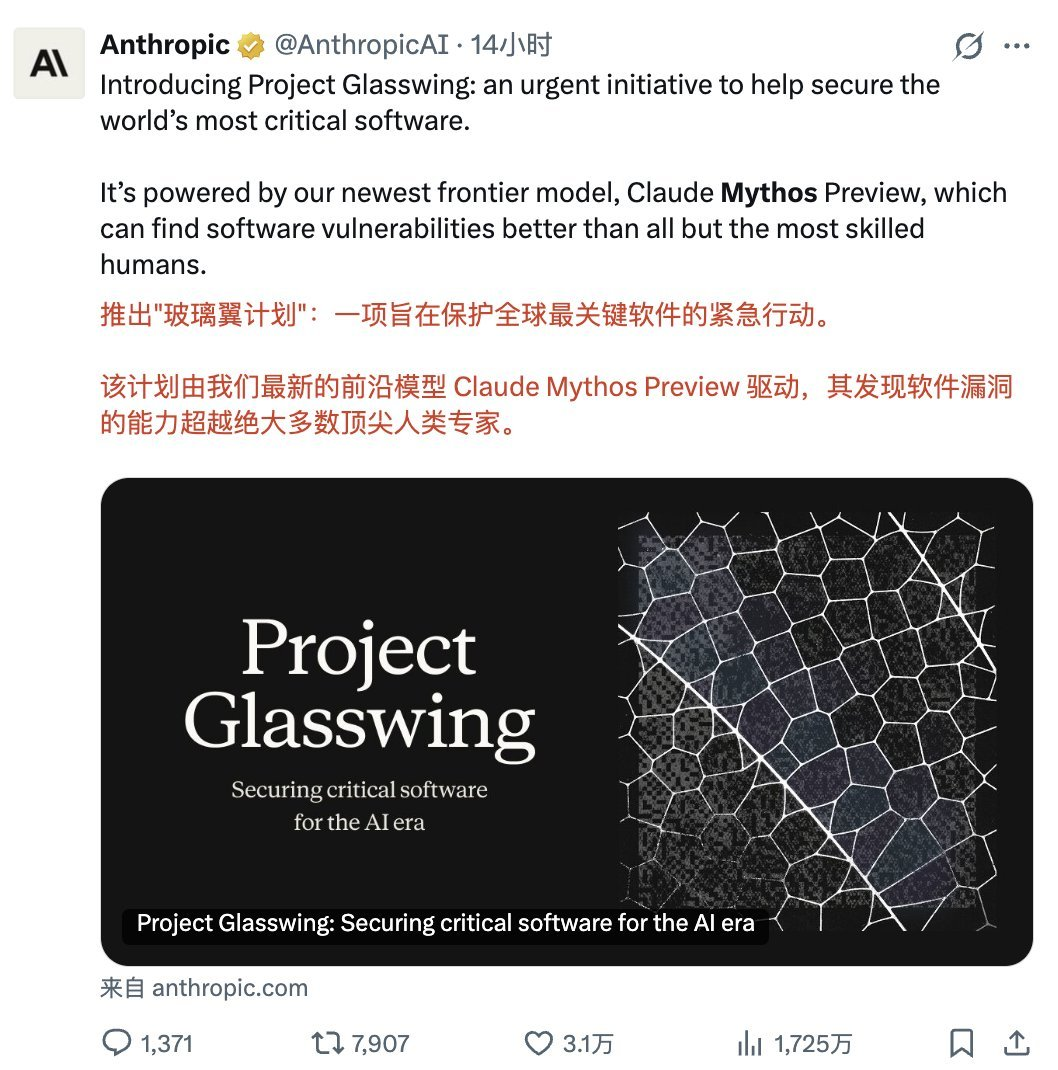
This large-scale model has been released in a preview version and may see limited enterprise applications in the future.
This implies that for just a few hundred or thousand dollars, you could essentially have a top-tier global cybersecurity team at your disposal.
With technological progress, it won't be long before more large models acquire this capability. In a matter of months, users might be able to surpass human hackers and cybersecurity experts using open-source large models, free of charge.
If autonomous offensive capabilities can be realized, then autonomous defensive capabilities will naturally follow suit.
For all cybersecurity companies, a paradigm shift is underway.
As early as the onset of the global AI wave sparked by ChatGPT in 2023, Xingkongjun has been closely monitoring the significant transformations within the cybersecurity industry.
Today, the industry stands at another crucial turning point: AI large models are revolutionizing the landscape of cybersecurity attacks and defenses.
This marks a pivotal moment for the cybersecurity sector.
Post-2025, it's not that traditional security products will become obsolete, but rather that the rules of engagement have fundamentally shifted—from rule-driven to AI-driven, from labor-intensive tactics to intelligent confrontation. For security vendors still relying solely on firewalls and IDS without innovation, the challenge has escalated significantly.
01
Is Venustech Ready for the Change?
On April 13, 2026, Venustech Group Co., Ltd. (002439.SZ) released its 2025 annual report. Revenue stood at RMB 2.338 billion, down 29.49% year-on-year; net profit attributable to shareholders was a loss of RMB 572 million, widening by 152.90% year-on-year.

Data Source: iFind
Against the backdrop of AI large models sweeping across industries, this leading domestic cybersecurity company is experiencing unprecedented transformational challenges. Despite declining revenue and widening losses, improved cash flow and breakthroughs in AI business present a mixed picture.
This is a battle for survival and a breakthrough for the future. Can Venustech transform amid these challenges?
However, one indicator has caught Xingkongjun's attention.
Net operating cash flow was RMB 287 million, up 191.07% year-on-year, marking a significant turnaround from negative to positive.
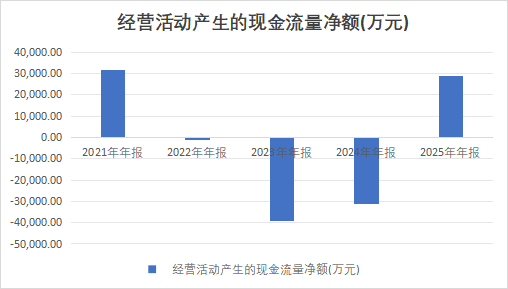
Data Source: iFind
Cash flow is the lifeblood of a company. Despite declining revenue and widening losses, the substantial improvement in operating cash flow indicates that the company's ability to collect payments and operational efficiency are on the rise.
Data disclosed in the annual report confirms this: Venustech has seen a decline in accounts receivable for eight consecutive quarters, with significantly improved sales collection efficiency. During the reporting period, the three main expenses (selling, administrative, and research and development) decreased by 8.68% year-on-year, showing the initial effects of refined management.
However, the fact of declining revenue cannot be overlooked.
Revenue of RMB 2.338 billion, compared to RMB 3.315 billion in 2024, represents a decrease of nearly RMB 1 billion. This is a rare and significant revenue decline for Venustech in recent years.
02
The Revenue Conundrum: Proactive Adjustment or Passive Contraction?
In 2025, Venustech's revenue declined by 29.49%, from RMB 3.315 billion to RMB 2.338 billion.
The primary reason for the revenue decline is the phased adjustment in business collaboration with China Mobile.
Venustech admitted in its annual report: "Business collaboration with China Mobile is undergoing structural optimization and quality and efficiency improvement. Although the total amount of related-party transactions has decreased year-on-year, the revenue from higher-quality self-procurement business by China Mobile has increased year-on-year, marking a shift from scale expansion to quality and efficiency upgrades."
In simpler terms, China Mobile, the "major client," has altered its procurement model. Shifting from past total package integration to a self-procurement-focused approach, Venustech is receiving less revenue from integration projects but more from direct sales of core products. This shift has indeed impacted revenue scale in the short term but is beneficial for improving gross margin and profitability in the long term.
At the same time, the company's proactive adjustment of low-margin integration business is also a significant factor in the revenue decline.
Integration business in the cybersecurity industry is essentially manual labor, involving "laying network cables and installing equipment," with low margins, long payment terms, and difficulty in collecting payments. Venustech proactively contracted this part of the business in 2025, resulting in lower revenue but improved business quality.
Another easily overlooked factor is the impact of industry cycles.
2025 marks the final year of the "14th Five-Year Plan," with generally tightened IT budgets for government and state-owned enterprises, leading to a slowdown in overall growth in the cybersecurity industry. As an industry leader, Venustech is the first to feel the effects.
However, short-term revenue decline does not equate to long-term loss of competitiveness.
Venustech clearly stated in its annual report that the company is "shifting from scale expansion to quality and efficiency upgrades." Although this proactive adjustment is challenging, it may be necessary for long-term success.
03
AI Breakthrough: A New Security Paradigm in the Era of Large Models
Despite overall performance pressure, Venustech has achieved significant breakthroughs in AI security deployments.
In 2025, the company's R&D investment accounted for 31.19% of revenue, maintaining a high proportion despite the revenue decline, indicating management's strong emphasis on technological innovation.
What are Venustech's core advancements in AI security?
The launch of the Model Application Firewall (MAF) is the most notable achievement.
This is a new category innovatively proposed by Venustech, specifically designed for the security protection of large model applications. MAF can effectively defend against new types of attacks targeting large models, such as prompt injection, data poisoning, and model theft, providing comprehensive security protection for large model applications.
The annual report disclosed that MAF "has become a new category recognized by the industry, setting a technological benchmark for AI application security." This means Venustech has taken the lead in the new track of AI security.
The "Anxing Intelligent Agent Matrix" is another important deployment.
Based on the Taihe Cybersecurity Large Model, Venustech has built an intelligent agent matrix covering core products such as situation awareness, threat intelligence, security detection, application protection, and data security. These AI agents can autonomously complete tasks such as security analysis, threat assessment, and response disposal, significantly improving the efficiency of security operations.
For example, Xingkongjun tested Venustech's AI security operations platform and found that its accuracy in threat detection and response speed were significantly improved compared to traditional rule engines. Although it cannot completely replace human labor, it can already handle 80% of routine security operations tasks.
Expansion into the personal and home (toC/toH) markets is also accelerating.
Venustech launched a secure cloud computer solution, achieving tens of millions in revenue and millions in monthly active users. This is an important attempt for the company to expand from traditional government and enterprise markets to consumer markets.
However, some issues were identified during testing. User willingness to pay for consumer-grade security products is low, with most users still accustomed to "free use." How to establish a sustainable business model in the C-end market is still being explored by Venustech.
04
China Mobile Collaboration: From Honeymoon to Adjustment Phase
The strategic collaboration between Venustech and China Mobile was one of the most significant partnerships in the industry in 2022. China Mobile Capital became the company's largest shareholder with a 23.37% stake, while the stake held by Wang Jia and Yan Li, a couple, decreased to about 22%.
Now, this "marriage" has entered its third year, transitioning from the honeymoon phase to an adjustment period.
What progress has been made in their collaboration in 2025?
The Dedicated Line Guardian product has served 72,000 government and enterprise clients, defending against over 100,000 attacks daily.
This is a successful case of integrating Venustech's security capabilities with China Mobile's dedicated line business. By embedding security capabilities into mobile dedicated lines, Venustech provides small and medium-sized enterprises with an integrated "network + security" service, achieving scalable and inclusive security services.
The development of an intensive password service and cloud-native security system based on Mobile Cloud is also progressing.
Venustech's security capabilities are deeply integrated with Mobile Cloud, providing native security protection for cloud customers. This "cloud-network-security" integrated model is the core direction of their collaboration.
However, the challenges of collaboration are also evident.
The annual report admitted that "the total amount of related-party transactions between the two parties has decreased year-on-year," directly leading to Venustech's revenue decline. Shifting from past large-scale integration projects to current selected projects, China Mobile's requirements for suppliers are increasing, and Venustech also needs to adapt to this change.
Simply put, China Mobile is no longer the "wealthy but naive" major client but demands that suppliers provide truly valuable products and services. This shift is challenging for Venustech in the short term but beneficial in the long term.
When China Mobile completes the optimization and upgrading of its supply chain, suppliers with true technological strength will gain a larger market share, while integrators relying on relationships will be eliminated. Whether Venustech can succeed in this reshuffle depends on the strength of its products and technologies.
05
The Certainties and Uncertainties of AI
For Venustech, AI security may be that sufficiently long slope, and the 31.19% R&D investment ratio is the sufficiently wet snow. Venustech is currently in the difficult climbing stage of rolling a snowball.
The 2025 annual report, although disappointing in terms of revenue and profit, indicates necessary transformations through improved cash flow, breakthroughs in AI business, and deepened collaboration with China Mobile.
Shifting from scale expansion to quality and efficiency upgrades, from integration business to product business, and from traditional security to AI security—these three transformations, although challenging, may be the necessary path for Venustech to achieve long-term healthy development.
Let's wait and see whether this leading domestic cybersecurity company can transform amid these challenges and secure a place in the security battlefield of the AI era.
The show, perhaps, has just begun.
-END-
Disclaimer: This article is based on the public company attributes of listed companies and core analysis and research based on information disclosed by listed companies in accordance with their legal obligations (including but not limited to interim announcements, periodic reports, and official interaction platforms); Shiyu Xingkong strives for fairness in the content and views of the article but does not guarantee its accuracy, completeness, or timeliness; the information or opinions expressed in this article do not constitute any investment advice, and Shiyu Xingkong is not responsible for any actions taken due to the use of this article. Copyright Notice: The content of this article is original to Shiyu Xingkong and may not be reproduced without authorization.