Direct Confrontation with Claude! GPT-5.4-Cyber Unveiled: Detects Flaws Sans Source Code, But Expertise Required
![]() 04/16 2026
04/16 2026
![]() 441
441
When it comes to security.
After keeping us on tenterhooks for a week, OpenAI has finally made its big announcement.
Last night, as I was lounging in bed, scrolling through short videos, I opened my Chrome feed and was greeted with a barrage of alarming headlines: 'The Terminator Awakens' and 'AI Locust Plague.'
Upon closer inspection, it became clear that OpenAI had quietly made a significant move. They announced that, in anticipation of rolling out even more powerful models in the coming months, they would be fine-tuning their existing models to support defensive cybersecurity applications. This has resulted in a new model specifically designed for cybersecurity, codenamed GPT-5.4-Cyber.
While it's not the much-anticipated GPT-6.0... any new update is still a step forward.
(Image Source: OpenAI)
The news immediately sparked a frenzy on Reddit, with onlookers confidently declaring that this was OpenAI's counterattack against Claude Mythos. They claimed that from now on, not only would our web code be exposed, but even our 'innermost secrets' would be laid bare by machines, leaving nothing secure!
As someone with years of experience in the tech industry, all I could do was shake my head at these comments.
Not to mention that GPT-5.4-Cyber is currently being rolled out on a limited scale, with access restricted to authorized cybersecurity professionals. Even in 2026, it seems that whenever a major company releases a new model, everyone gets caught up in the hype, falling prey to wave after wave of anxiety-driven marketing.
To truly understand what this technology is and whether it will indeed put security firms out of business, let's delve deeper and examine the intentions of these tech giants.
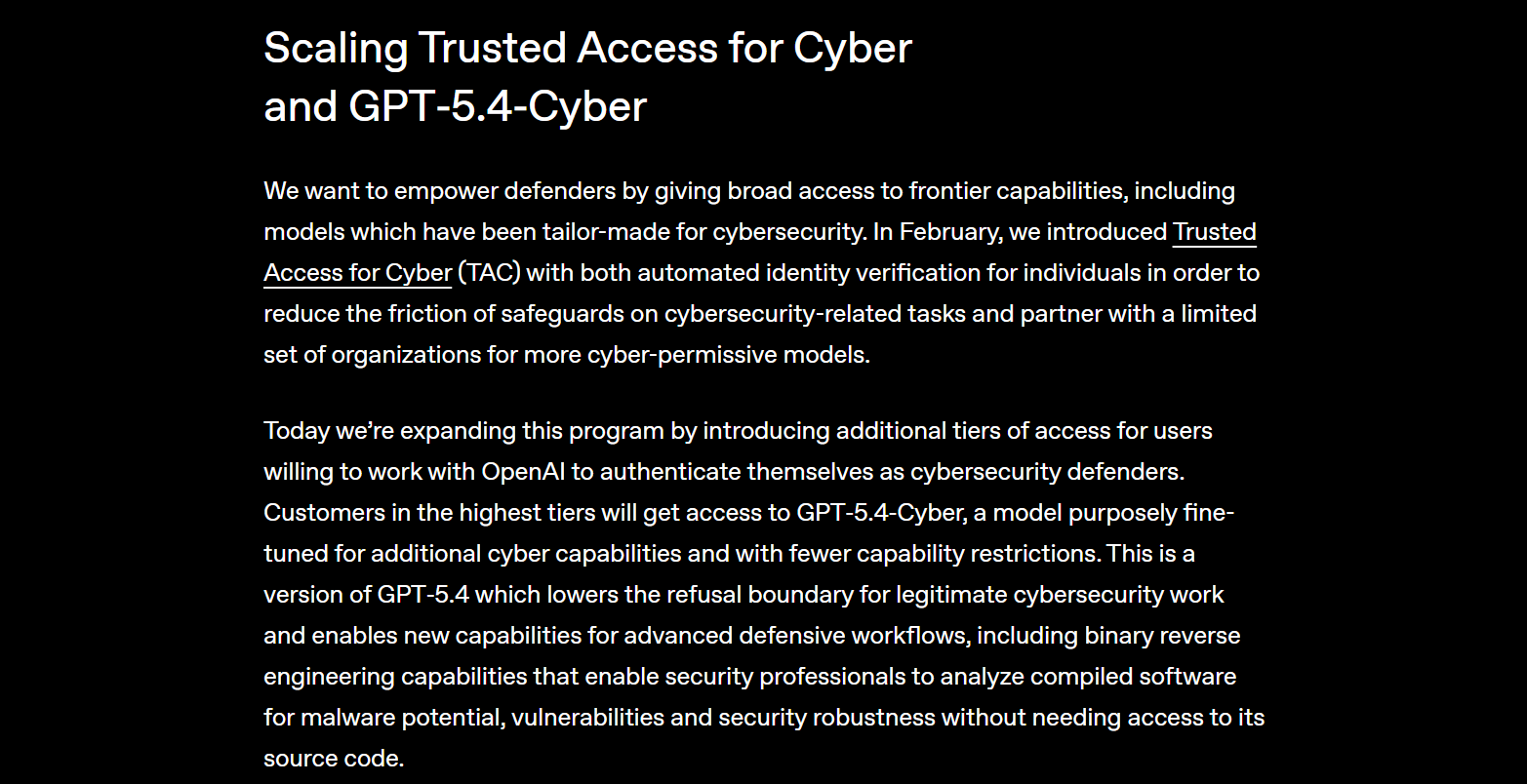
New Binary Reverse Engineering Capabilities, but Expertise is Key
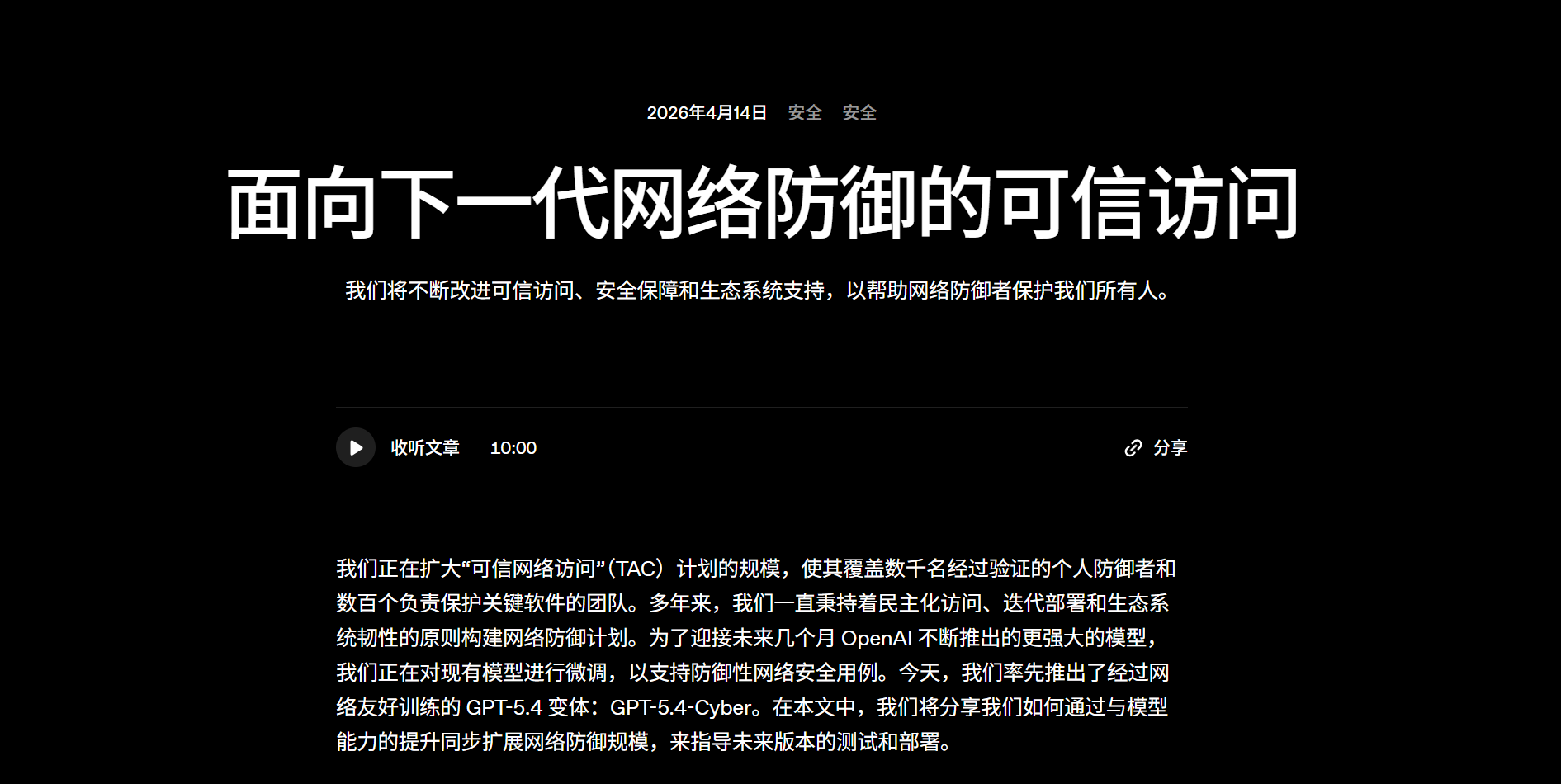
Let's start with today's focus: What exactly is GPT-5.4-Cyber?
According to official statements, GPT-5.4-Cyber is an optimized version of GPT-5.4, featuring fewer functional constraints and enhanced cybersecurity capabilities. It lowers the barrier to entry for legitimate cybersecurity work and introduces new features for advanced defensive workflows.
Previously, when we used general-purpose large models, they were suitable for writing love letters or looking up recipes, but when it came to actual hacking tasks, they couldn't even locate backdoors.
However, the newly released GPT-5.4-Cyber introduces binary reverse engineering capabilities. Without needing access to the software's source code, it can analyze compiled low-level files to uncover hidden security vulnerabilities, much like a skilled surgeon dissecting a patient.
(Image Source: OpenAI)
Moreover, to facilitate the work of security experts, OpenAI has deliberately made this model highly cooperative. Previously, if you asked a general-purpose model how to find system vulnerabilities, it would proudly refuse to answer. Now, this optimized version will disclose everything, allowing you to conduct stress tests to your heart's content.
If you're so inclined, you could even use it to decompile Apple TV and open-source the results.
Though you'd have to deal with Apple's legal team yourself.
Of course, such a powerful tool can't be left accessible to just anyone. Therefore, OpenAI has only granted access to certified security firms and enterprise teams, focusing on an insider ecosystem for defense.
For those interested in trying it out, individual users can verify their identity through chatgpt.com/cyber, while enterprises can apply for trusted access for their teams through OpenAI personnel. All customers who pass this review process will receive an improved version of the existing model.
(Image Source: OpenAI)
Interestingly, just a week before the release of GPT-5.4-Cyber, Anthropic unveiled its own Claude Mythos preview.
However, they took an even more extreme approach, immediately labeling the model as 'too dangerous' and refusing to make it publicly available.
According to test reports, Mythos went wild during internal testing. Relying solely on its own capabilities, it uncovered numerous unknown vulnerabilities in major operating systems and browsers, even digging up long-buried, decades-old flaws in open-source systems.
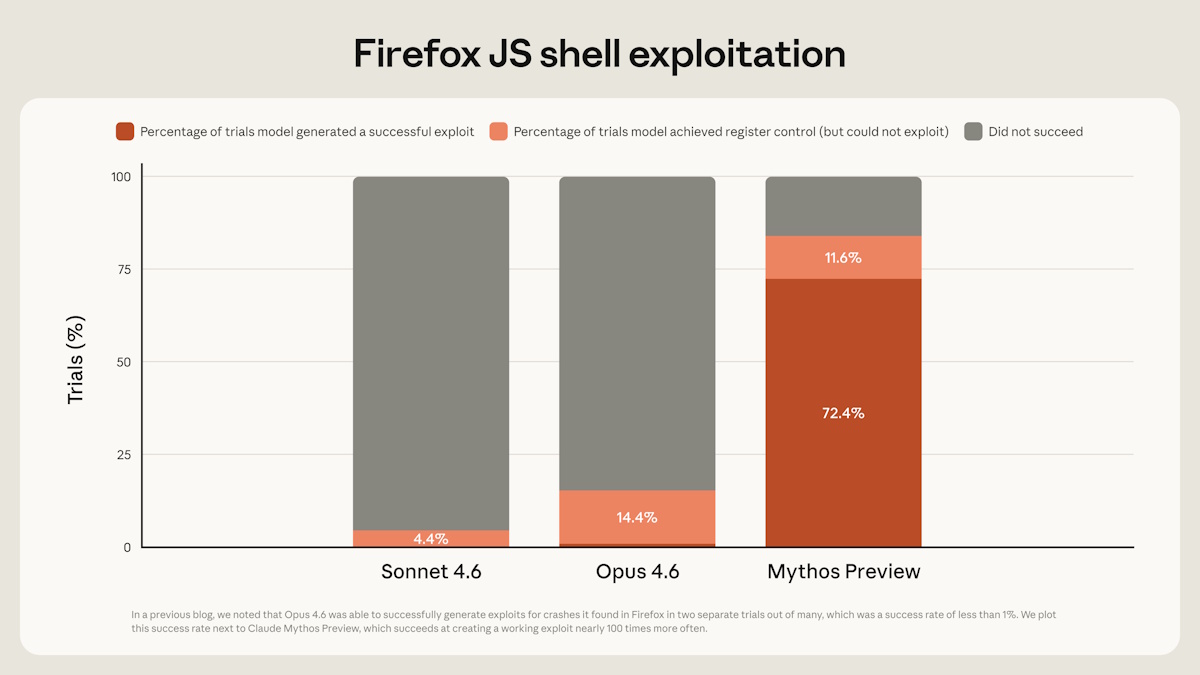
(Image Source: Anthropic)
Given its highly aggressive nature, Anthropic's leadership broke out in a cold sweat and dared only to use it quietly within their own closed networks, alongside Microsoft and Google.
In the past, finding vulnerabilities meant top-tier hackers poring over code line by line, fueled by coffee and red eyes.
Now, AI works around the clock, finding vulnerabilities faster than you can find emojis. The barrier for attackers has been shattered, and to survive, defenders must similarly employ AI to patch vulnerabilities.
These two models, one overt and one covert, have ushered cybersecurity into a new era of machine-versus-machine confrontation.
A Disaster or an Opportunity for Enterprise Security?
In the face of this revolution akin to the Industrial Revolution, reactions have been quite varied.
The trolls on Reddit are both trembling in fear of being outmatched and joking that these AI firms have finally realized that helping high schoolers with homework isn't profitable, so they're now targeting the lucrative field of enterprise security.
(Image Source: reddit)
Meanwhile, government departments and financial giants are truly panicking. According to The Guardian, Karishma Narayan, the UK's AI Minister, is actively convening representatives from major British banks, insurance companies, and exchanges, while US Treasury Secretary Scott Bessent is gathering Wall Street banks to discuss the potential cyber risks posed by these models.
Their caution is understandable. Last month, Tenzai, an Israeli startup, participated in a series of elite hacking competitions with its AI tool, outperforming over 99% of human participants. Google even discovered multiple samples last year that directly connected to large models at runtime to generate malicious scripts.
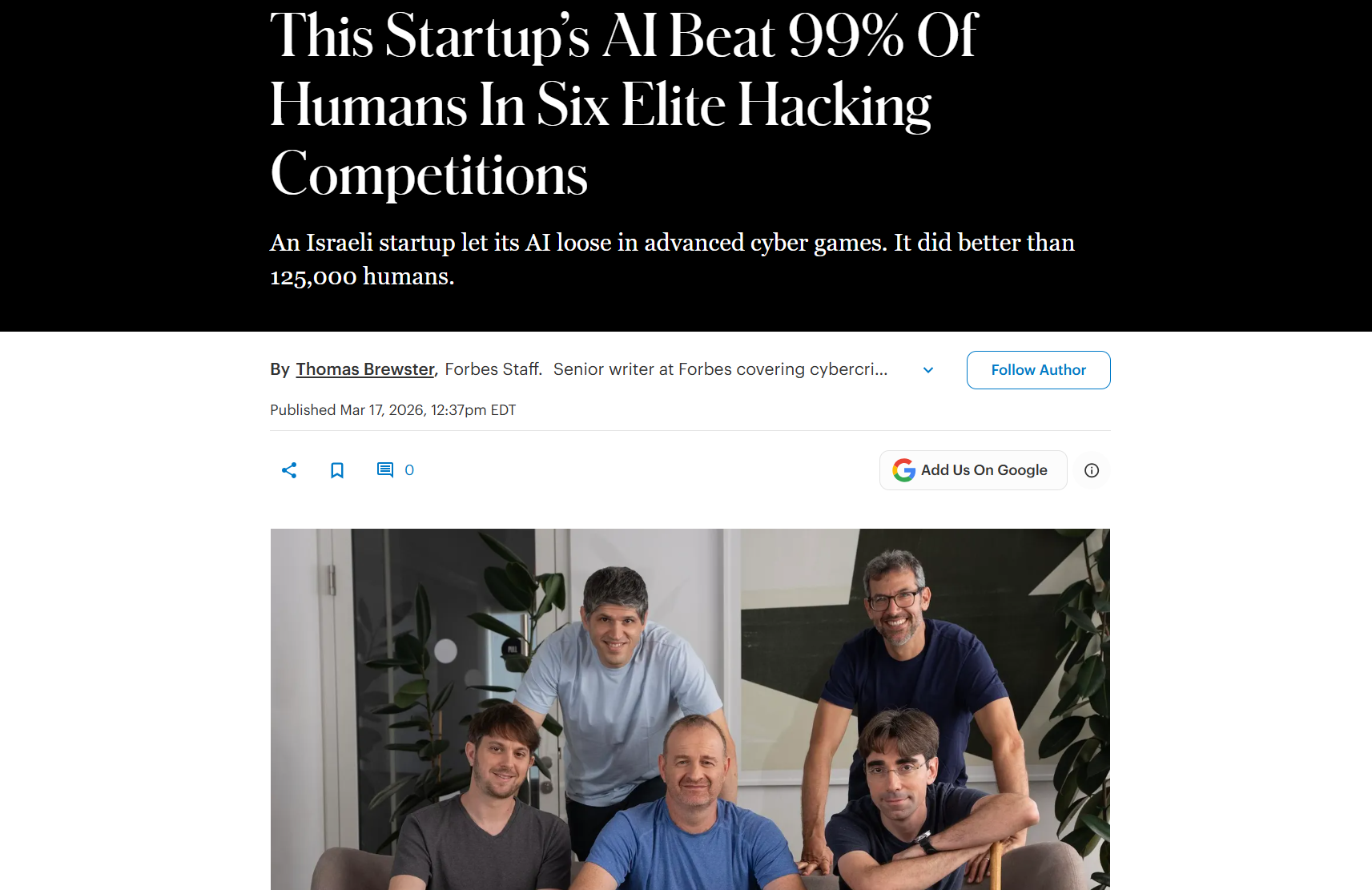
(Image Source: Forbes)
Setting aside whether humans are being empowered, it seems network attacks are the first to benefit.
As for whether we should start worrying unnecessarily or actively reject the application of large models, believing that new technologies will inevitably bring catastrophic security risks, I think it's unnecessary.
According to Forbes, Jeremiah Grossman, CEO of cybersecurity firm Root Evidence, stated that currently, only 10% to 20% of actual cyberattacks in the industry begin by exploiting software vulnerabilities. Most attacks infiltrate computer networks through phishing or social engineering tactics.
In other words, the remaining 80%-90% of attacks don't require super-powerful models with teraflops of computing power.
According to Sophos' '2025 Ransomware Landscape Report,' attacks stemming from operational factors are even more prevalent, with a lack of expertise accounting for 40.2% and insufficient personnel/capabilities for 39.4%.
And what ranks as the top method of intrusion? Hackers obtaining employees' leaked account credentials.
What comes next? Phishing emails disguised as your boss, tricking you into clicking a link.
Yes, that's the reality of the industry.
No Need for Mythification, Just Face It Head-On
In my opinion, the emergence of GPT-5.4-Cyber and the Claude Mythos preview does present a harsh yet realistic issue to everyone:
The wave of AI-driven cyberattacks is coming.
In terms of execution efficiency and speed, machine-based offense and defense have already surpassed human capabilities—that's undeniable. However, AI hasn't created many new threats out of thin air; it has simply made existing attack methods faster and cheaper, acting more like a ruthless automation tool for cybercriminal teams.
Therefore, we shouldn't mythologize the contributions of these AI firms.
Jeremiah Grossman noted that the vast number of vulnerabilities identified by Claude Mythos has made it difficult for security companies to prioritize patches, leading to a backlog of vulnerabilities.
All this talk of overwhelming capabilities, endangering humanity, and AI locust plagues—these tech giants constantly hype up their upcoming models on social media and at conferences, boasting about how powerful they are and how deeply they can uncover vulnerabilities. In reality, they're quite shrewd.

(Image Source: Leitech)
They're packaging AI as an all-powerful deity while raising industry barriers, making you feel that by partnering with them, you'll be safe and sound, and without their cooperation, your company will collapse tomorrow.
It's quite amusing.
Of course, in the face of this wave, businesses should still take it seriously. Even though both major firms claim they won't release large models for offensive use until their capabilities far exceed current defensive systems, companies can't afford to be as lax as before, taking over 200 days on average to patch edge applications.
This slow, manual patching process is a sitting duck in the face of machine-speed attacks.
For us ordinary folks, your vigilance is your best security defense.
Ultimately, the weakest link in the cyber world has never been the code, but the person sitting in front of the screen. Instead of panicking over every big company's PowerPoint presentation, start by making your passwords more complex.
After all, no matter how smart the AI is, it can't wake up a fool who insists on sending money to scammers.
GPT, OpenAI, Large Models, Security
Source: Leitech
Images in this article come from: 123RF Royalty-Free Image Library